Network Config Toolby JavanteaJuly 2, 2006 DESCRIPTION
A graphical network config tool for AltSciOS. This tool is in development and is mainly a theoretical discussion of how a network configuration tool should work to allow the easiest and quickest use. |
|
AltSciOS is currently in development and is written in Python. It was built for the PDA of a video game, called Hack Mars. It works very much like other Posix OS (Unix, Linux, and BSD). The back end looks very different, though.
Although AltSci Net does not currently exist, a suitable replacement currently exists called Tor.
Gateways serve two purposes: 1) as a remote shell, and 2) as a VPN. It allows scripted communications, which is quite necessary for long distance networking (latency = 90 minutes). It also hides the traffic among many other hacker's traffic. Since gateways are shared, any possible tracing goes back to "AltSci" which does not officially exist. Hackers connecting to a gateway have plausible deniability since plenty of legitimate uses exist for gateways. In fact, all legitimate use of the networks involve gateways. Gateways also allow multiple hackers to communicate without transferring any data publicly.
Gateways currently exist only as configurations of servers. A Linux/BSD server running SSH can do both of these if configured correctly. Setting up a VPN is not trivial, but should easy with this tool.
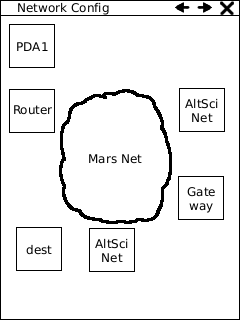
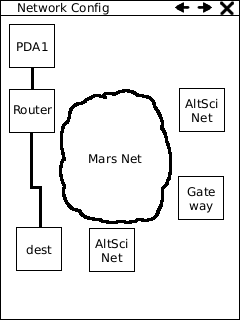
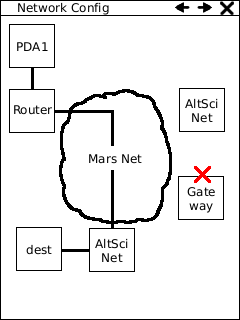
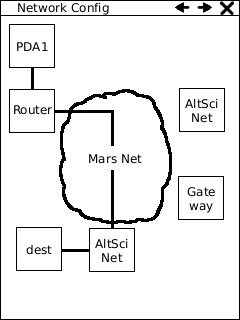
PDA1 connects to a router with a local network interface.
The router connects to AltSci Net via Mars Net.
All connections to AltSci Net are encrypted and anonymized so that they cannot be traced.
We connect to the gateway over AltSci Net. The gateway gives us a powerful system to script our communications. It is useful for extra anonymity and convenience (start a transfer at 9 am, pick it up at 10:30 am). All AltSci hackers have access to one or more gateways on the AltSci Network.
The gateway is a part of AltSci Net. The gateway goes down from time to time. AltSci Net only goes down when bad things happen on Terra and Mars. But it's mesh routing allows it to come back up soon after.
The gateway connects to the AltSci Net which encrypts and anonymizes the communication to the destination.
|
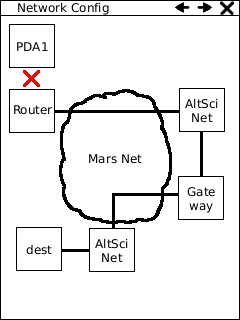
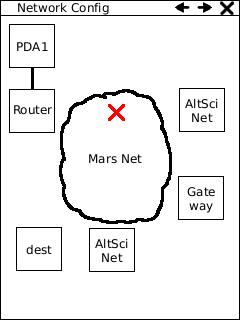
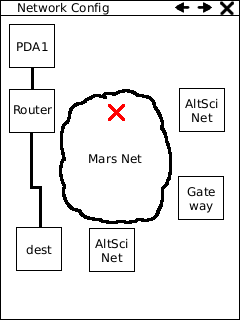
If the pda is not connected to a router, a red X shows up instead of a black line. The user can click the router or the X or the PDA1 to decide how to connect to a router. |
 |
|
 |
|
|
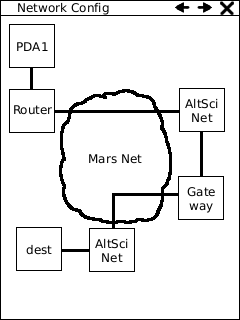
At any time, a user can click the destination host to connect directly to local area hosts. |
|
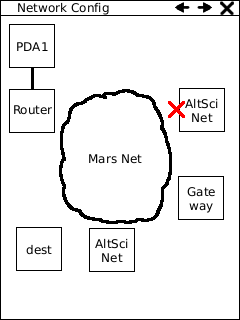
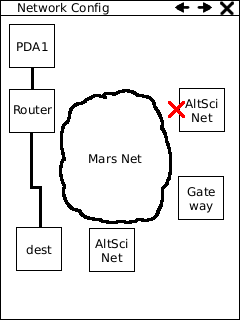
If your gateway is down, a red X shows up next to it. The user can click the AltSci Net to connect to destination hosts indirectly while a gateway is down. If the destination host is remote, the local host must stay online until the response is received. If a man in the middle attacker knows the timestamps on the packets outgoing packet and the incoming packet on the destination server, s/he will be able to say with some probability that the person in question is the origin. Even though AltSci Net protects the identity of the local host from an attacker who is watching one side of the transaction and not the other, it cannot protect the identity of the local host if an attacker has the timestamps. This is known as a side-channel attack. |
|
At any time, a user can click the AltSci Net to connect to destination hosts indirectly. This allows encryption and anonymity without requiring access to the gateway, which might be overkill for simple activities. While the convenience and power of a gateway is lost, the usefulness remains. |
| At any time, a user can click the router to choose a different network route. A host may be connected to any number of routers using the setup. |
| At any time, a user can click the AltSci Net to configure which routes are chosen at a certain point of time. |
| At any time, a user can click the gateway to configure use of the gateway. |
| At any time, a user can click Mars Net to run diagnostics. |
-
Leave a Reply





Comments: 0
Leave a reply »