Git repository: git clone https://www.altsci.com/repo/javre.git
| jvoss@altsci.com
Talk
Read the Talk
Slides. Video and paper coming soon.
Examples
See the
solution to kicker of elves from Vancouver BSides 2015 CTF at Neg9.org.
See the full tutorial at AltSci Concepts.
# Disassemble black stripped of symbols
python disasm1.py black_release >black_release.jav
less black_release.jav
...
.text:
400800: PUSH RBP
400801: MOV RBP, RSI
400804: PUSH RBX
400805: SUB RSP, 0x418
40080c: MOV RAX, [FS:0x28]
400815: MOV [RSP+0x408], RAX
40081d: XOR EAX, EAX
40081f: CMP EDI, 0x2 ;
400822: JZ 0x400833 ; if(EDI != 0x2) {
400824: MOV ESI, 0x400bd0 ; 'usage: usb_printerid /dev/usb/lp0\n'
400829: MOV EDI, 0x1 ; '\x01'
40082e: CALL 4009d0 <error>
; }
400833: MOV RDI, [RBP+0x8]
400837: XOR EAX, EAX
400839: MOV ESI, 0x2 ; '\x02'
40083e: CALL 4007b0 <open>
400843: TEST EAX, EAX ;
400845: MOV EBX, EAX
400847: JS 0x4008a9 ; if(EAX >= 0) {
400849: XOR EAX, EAX
40084b: MOV RDX, RSP
40084e: MOV ESI, 0xffffffff84005001
400853: MOV EDI, EBX
Documentation
disasm1.py
Usage: python disasm1.py [-h] [--verbose] [filename]
Disassemble an ELF file.
positional arguments:
filename an ELF file
optional arguments:
-h, --help show this help message and exit
--verbose, -v
- disassemble(data, printFunction, printErrorFunction)
- data is a byte array with the ELF file.
printFunction is a function that takes the following arguments:
(sect_name, sect_disasm, dynsym_addrs, dynsym_names)
printErrorFunction is a function that takes the following arguments:
(*args, **kwargs)
That's right, it should be a wrapper for print.
- printDisassembly(sect_name, sect_disasm, dynsym_addrs, dynsym_names, elf_st, sections, progs, data)
- Print the disassembly to stdout. This function is passed to disassemble.
- printError(*args, **kwargs)
- The correct way to wrap print. This function is passed to disassemble.
- deref(addr, data, elf_st, sections, progs)
- cmpToC(cmpInstr, jmpStr, inverse=True)
- Example:
cmpToC([0, '1234', 'CMP [RBP-0x4], 0x1'], 'JG 0x4005b4')
TODO: this whole function is based on my guesses.
FIXME: signed needs research.
inverse is for while loops where logic is inverse.
- InstrToC(instr)
-
Experimental Decompilation support.
Inputs one tuple with (addr, length, instruction_mnemonic) in the
format that distorm gives.
Outputs None or a tuple with (comment to append to asm, python_object)
python_object allows a person to understand what is going on so that
they can reproduce the effect in python. For example:
python_object = AsmNoop() allows a person to query what happens to EBX?
We can say that EBX is ebx.
python_object.stepEBX(44) == 44
- bfd_elf_get_synthetic_symtab(sections, section_names, data, plt_section)
- A few simple things, most important is the parsing of .rela.plt.
It allows us to get the correct function names for .plt.
See rel.plt.py for the c code it's trying to replace.
- demangle(s)
- An attempt to demangle. The C version of demangle in binutils is 5000
lines so I won't get a very good coverage in 100 lines.
c++filt is a quick solution to this, but calling c++filt thousands of
times is very inefficient.
_Z21LoadLocalAchievementsv
_Z1fs
_ZSt16__throw_bad_castv
_ZNSs6appendEPKcm
_ZNKSs16find_last_not_ofEPKcmm
_ZSt18_Rb_tree_decrementPKSt18_Rb_tree_node_base
FIXME: _ZNSt8ios_base4InitC1Ev
P is pointer
K is const
c is char
s is short
m is unsigned long
St is std::
NSs is std::basic_string<char, std::char_traits<char>, std::allocator<char> >::
E is currently unknown.
- dl_new_hash(s)
- "Dan Bernstein's string hash function posted eons ago on comp.lang.c."
https://sourceware.org/ml/binutils/2006-10/msg00377.html
- elf_x86_64_plt_sym_val(i, plt_vma, rel)
- elf_x86_plt_sym_val(i, plt_vma, rel)
- i386 and x86-64 are the same. Surprise.
- main()
- This function is called when you run disasm1.py on the command line. It calls disassemble().
elf1.py
Usage: python elf1.py [filename]
This library parses ELF files. It contains a simple test function that prints the contents of headers.
ELF Parser
by Javantea
Aug 2007 for virus8a.py
Simply read an ELF file. No funny business.
Currently only reads 32-bit and 64-bit ELF files in little endian.
class elf_header
/sbin/grub 32-bit x86
00000000 7f 45 4c 46 01 01 01 00 00 00 00 00 00 00 00 00 |.ELF............|
simple 64-bit x86-64
00000000 7f 45 4c 46 02 01 01 00 00 00 00 00 00 00 00 00 |.ELF............|
class prog_header
class section_header
- __init__(self, data, elf, i, error=None)
- __str__(self)
- out(self)
- setFlags(self, w, a, x)
- Write, alloc, execute
sh_flags Sections support one-bit flags that describe miscellaneous attributes. If a flag
bit is set in sh_flags, the attribute is "on" for the section. Otherwise, the
attribute is "off" or does not apply. Undefined attributes are set to zero.
- setName(self, data, sect)
- main()
- parseELF(data, error=None)
gtk-javre.py
Usage: python gtk-javre.py [filename]
This GUI program disassembles an ELF file just like disasm1.py and displays it with syntax highlighting. It has open and save buttons so that you can save anything you reverse.
Of course, you can't reopen files yet. Many reverse engineering tools are going to be added to this interface.
class JavREWindow(Gtk.Window)
Javantea's Reverse Engineering Tool window
Contains everything in that window.
- __init__(self)
- on_reverse_clicked(self, widget)
- on_file_chosen(self, widget, filename)
- on_save_clicked(self, widget)
- on_outfile_chosen(self, widget, filename)
- textArea_tooltip(self, widget, x, y, keyboard_mode, tooltip)
- disasmToBuffer(textBuffer, sect_name, sect_disasm, dynsym_addrs, dynsym_names, elf_st, sections, progs, data)
- Based on disasmToString
- disasmToString(sect_name, sect_disasm, dynsym_addrs, dynsym_names, elf_st, sections, progs, data)
- Based on printDisassembly from disasm1.py
- doNothing(sect_name, sect_disasm, dynsym_addrs, dynsym_names, elf_st, sections, progs, data)
- disasm1.disassemble wants a function like this. Here it is.
- main()
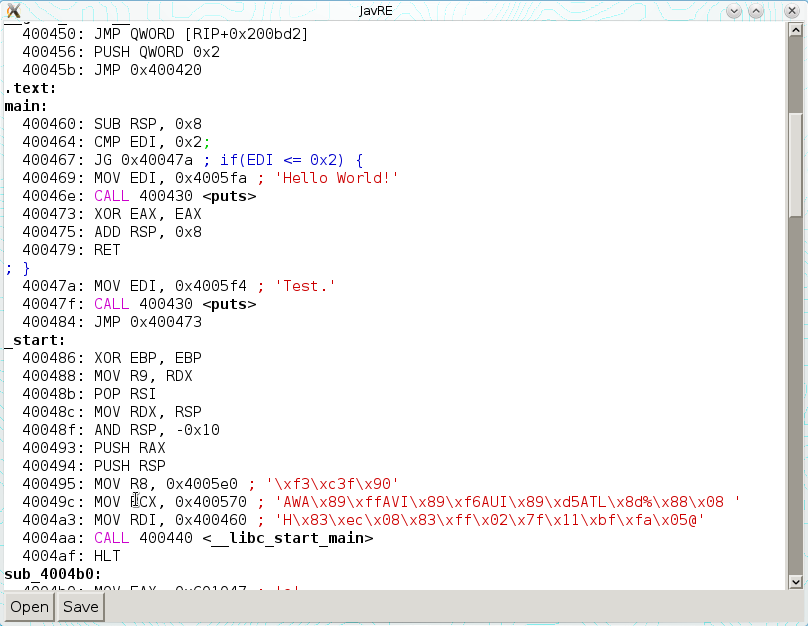
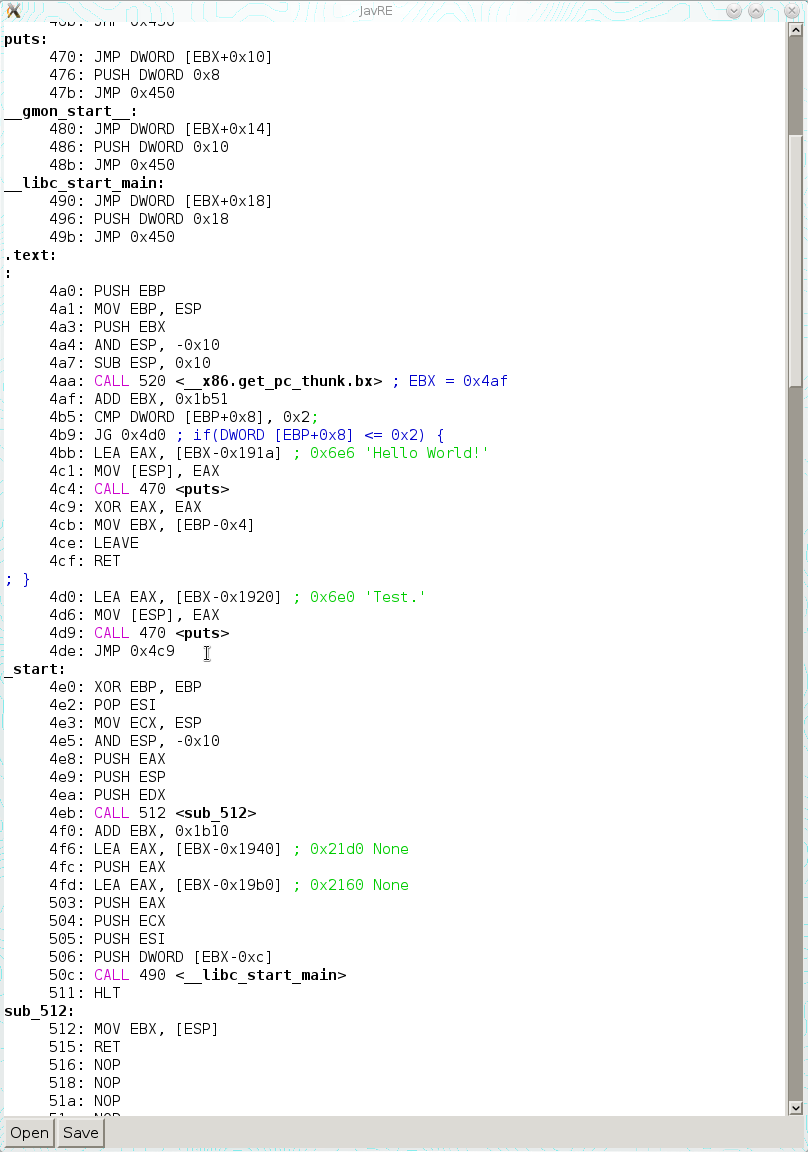
Screenshots
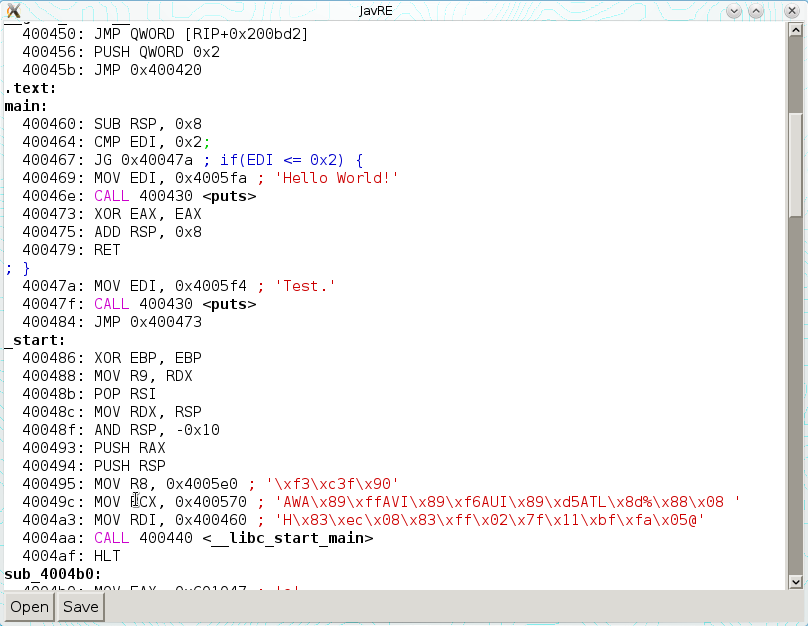
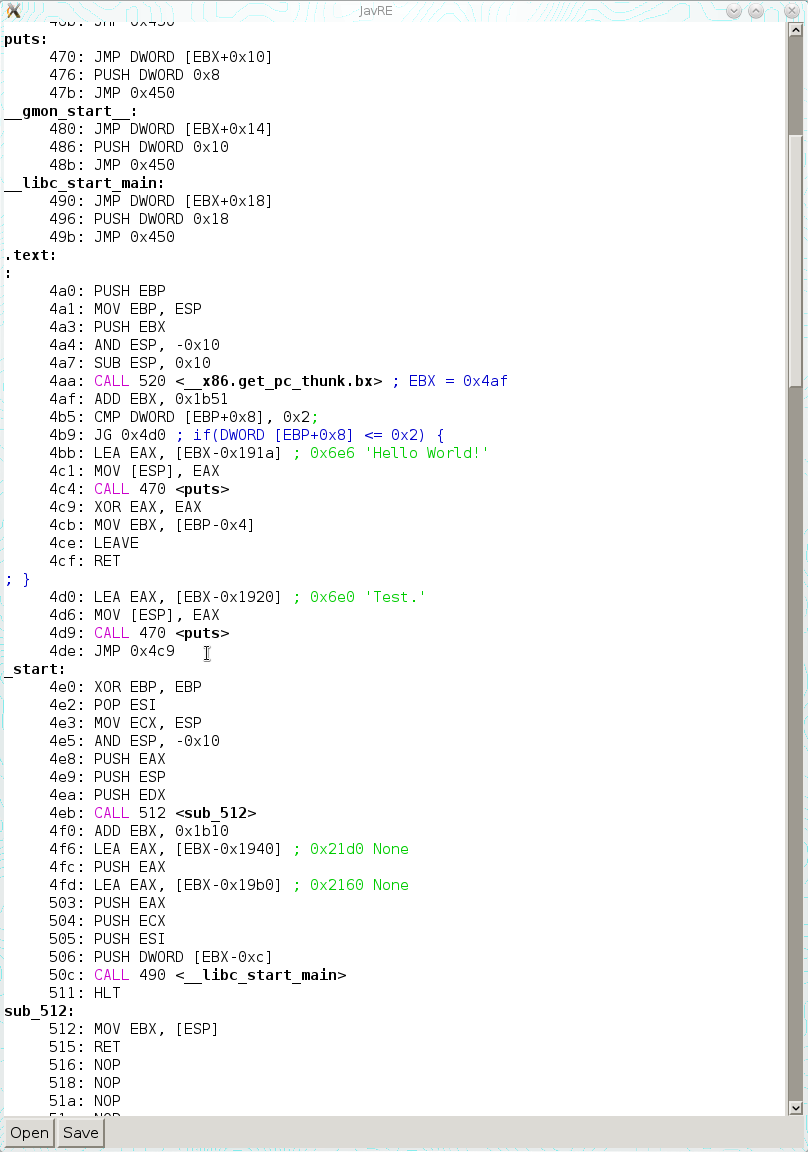
2015-02-02
Computer Journal